Table of Contents
Using FIRE's Spotlight Database
Research & Learn
FIRE is proud to offer the only database of United States college speech policies, the Spotlight Database. FIRE rates more than 475 of the nation’s top colleges and universities, so navigating the system can be intimidating. With that in mind, we present the following guide to using our database.
FIRE’s Speech Code Ratings
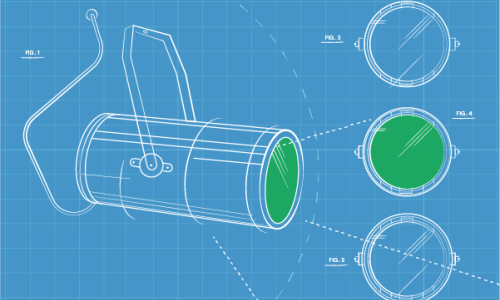
Next to each rated school in our database, you will see a colored traffic light—red, yellow, green, or blue (the last is reserved for universities that earn a “Warning” rating from FIRE, as explained in detail below). Each individual policy will also receive a red, yellow, or green light. This is FIRE’s Speech Code Rating System, which informs you of FIRE’s opinion of the degree to which free speech is curtailed at a particular institution.
The Speech Code Rating System applies equally to public and most private universities. While private institutions are not directly legally bound to uphold the Constitution, those that promise debate and freedom are morally bound—and may be contractually bound, depending on the circumstances—to uphold the fundamental principles of free speech and of academic freedom, principles that underlie the First Amendment. Read more on the distinction between public and private schools.

Red Light
A “red light” institution has at least one red light policy that both clearly and substantially restricts freedom of speech. A “clear” restriction is one that unambiguously infringes on what is, or should be, protected expression. In other words, the threat to free speech at a red light institution is obvious on the face of the policy and does not depend on how the policy is applied.
In addition, when a university restricts access to its speech-related policies by requiring a login and password, it denies prospective students and their parents the ability to weigh this crucial information. At FIRE, we consider this action by a university to be deceptive and serious enough that it alone warrants a “red light” rating.
At public institutions, red light policies are unconstitutional.

Yellow Light
A “yellow light” institution has at least one yellow light policy that restricts a more limited amount of protected expression or, by virtue of vague wording, can too easily be used to restrict protected expression.
For example, a ban on “posters containing references to alcohol or drugs” violates the right to free speech because it unambiguously restricts speech on the basis of content and viewpoint. However, its scope is very limited, so it may receive a yellow light.
Alternatively, a policy banning “verbal abuse” could be applied to prohibit a substantial amount of protected speech, but is not a red light violation because “abuse” might refer only to unprotected speech, such as harassment (as properly defined by law) or threats of violence. In other words, the extent of the threat to free speech would depend on how such a policy is applied.
At public institutions, yellow light policies are unconstitutional.

Green Light
If a college or university’s policies do not seriously imperil speech, that college or university receives a “green light.” A green light does not by itself guarantee that a school actively supports free expression. It simply means that FIRE is not currently aware of any serious threats to students’ free speech rights in the written policies on that campus. Individual policies that do not threaten free expression also receive green light ratings.

Warning - Does Not Promise Free Speech
FIRE believes that free speech is not only a moral imperative, but also an essential element of a college education. However, private universities are just that—private associations—and as such, they possess their own right to free association, which allows them to prioritize other values above the right to free speech if they wish to do so. Therefore, when a private university clearly and consistently states that it holds a certain set of values above a commitment to freedom of speech, FIRE warns prospective students and faculty members of this fact.
How FIRE Determines Overall School Ratings
To determine a school's overall rating, FIRE employs the following system:
- In order to earn an overall green light rating, a school must not maintain any policies that earn a red or yellow light rating.
- A school earns an overall yellow light rating if it maintains at least one policy that earns a yellow light rating, but does not maintain any policies that earn a red light rating.
- Institutions receive an overall red light rating when they maintain at least one policy that earns a red light rating.
To be clear, FIRE does not produce an “average” of an institution’s policy ratings to determine an overall rating; a school with five yellow light policies and one red light policy earns an overall red light rating, just as a school with one yellow light policy and five red light policies earns an overall red light rating. (Aside from at green light schools, it is unusual for every policy at an institution to have the same rating.)
The one exception to this general rule is that, due to federal regulations, certain harassment policies may earn a yellow light rating without affecting an institution's overall green light rating. Title IX regulations that took effect August 14, 2020 direct institutions to adopt a definition of sexual harassment for purposes of Title IX proceedings that tracks the Supreme Court’s definition from Davis v. Monroe County Board of Education: “[u]nwelcome conduct determined by a reasonable person to be so severe, pervasive, and objectively offensive that it effectively denies a person equal access to the recipient’s education program or activity” (emphasis added).
However, the same regulations also provide that “inappropriate or illegal behavior may be addressed by a [school receiving federal funding] even if the conduct clearly does not meet the Davis standard or otherwise constitute sexual harassment under § 106.30, either under a recipient’s own code of conduct or under criminal laws in a recipient’s jurisdiction.” As a result, the majority of institutions whose policies we reviewed have adopted a sexual harassment definition tracking Davis for conduct falling under Title IX, while maintaining less stringent definitions for allegations of harassment that they believe fall outside of Title IX’s scope — most often banning conduct that is “severe or pervasive and objectively offensive,” using “or” rather than “and.”
FIRE strongly encourages institutions to adopt the Davis standard in all policies regulating peer harassment in order to comport with both the First Amendment and the spirit of the regulations. We will not award policies that do not adopt this full standard a green light rating. However, while the existing regulations remain subject to litigation and Department of Education review, policies earning a yellow light rating for utilizing a “severe or pervasive and objectively offensive” standard will not threaten an institution’s overall green light rating.
Accessing a School's Policies
When you select an institution, you will be directed to the entry for that college or university. Underneath the school’s basic information, you will find tabs labeled “Speech Codes,” “Cases,” “Articles,” and, for select schools, “Due Process” and “Campus Climate.” To see the school’s speech-related policies, click on the “Speech Codes” tab. For each speech code, you will see a relevant excerpt of the policy in question. Clicking “Read More” will take you to the full excerpt and a link to a PDF of the full policy.
The policies are sorted by rating: red light policies first, then yellow, then green. If a school earns a Warning rating, the policies reviewed by FIRE will display in no particular order.
Policy Types
Broadly speaking, there are two types of speech-related policies: restrictions on expressive rights and advertised commitments to free expression. FIRE further subdivides restrictions on expressive rights into the following categories:
- Harassment policies
- Policies on tolerance, respect, and civility
- Policies on “bias” and “hate speech”
- Bullying policies
- Protest and demonstration policies
- Posting policies
- Internet usage policies
- Policies restricting freedom of conscience
- Security fee policies
- Other speech codes
Ready to get going?